5.3 Safer networking habits
Blending rather than hiding
Network safety is often framed as hiding, but in everyday life the more practical goal is to blend. A laptop that behaves like a normal laptop, a phone that connects in a predictable way, and a household network that looks like a household network will generally attract less attention than one that is constantly trying to look unusual. Blending does not mean giving up privacy. It means choosing habits that reduce the number of sharp edges in your network footprint, so that normal use does not become a series of anomalies.
The key trade-off is that blending relies on consistency: your devices should behave in a steady, boring way. That can feel at odds with the idea of randomness or stealth. In practice, stability tends to be safer than novelty. When people get into trouble it is often because their setup is inconsistent: the laptop uses a VPN on Monday, no VPN on Tuesday, and a different VPN on Wednesday; the phone uses a rotating MAC address in a café but a fixed one on the train. Each shift can reveal more than a calm, consistent pattern would.
Public Wi‑Fi risks without drama
Public Wi‑Fi is convenient and cheap, but it is also shared infrastructure. The two common risks are interception and impersonation. Interception happens when someone on the same network can view unencrypted traffic, and impersonation happens when a network is set up to look like a legitimate hotspot. Both are real, and both are usually mundane: it is far more likely to be a bored hobbyist running a test than a targeted operation against you personally.
A practical example: you sit in a café and connect to “FreeCafeWiFi”. A person nearby runs a hotspot called “FreeCafeWiFi” too, hoping your phone joins theirs. Once connected, they can see DNS requests and any unencrypted traffic, and they can try to redirect you to fake login pages. Modern websites use HTTPS, which encrypts the contents of your session, but it does not hide the fact that you are visiting a site, nor does it protect you if you accept a dodgy certificate prompt in a rush.
Mitigations that actually work are simple. Prefer your mobile data connection when you are doing anything sensitive, because it is usually harder for strangers to interfere with. If you use public Wi‑Fi, check the network name with staff and avoid networks that require you to install apps or certificates. Use a reputable VPN if you already trust one, but do not assume a VPN makes an untrustworthy hotspot safe; it reduces certain risks but does not stop phishing or malware.
A common misunderstanding is that “HTTPS means public Wi‑Fi is safe”. HTTPS protects your page content, logins, and messages, but it does not protect the whole picture. The network can still see which sites you use, how often, and roughly when. It also cannot protect you from a malicious website or a fake login page that looks convincing. Treat public Wi‑Fi as a convenience, not a secure environment.
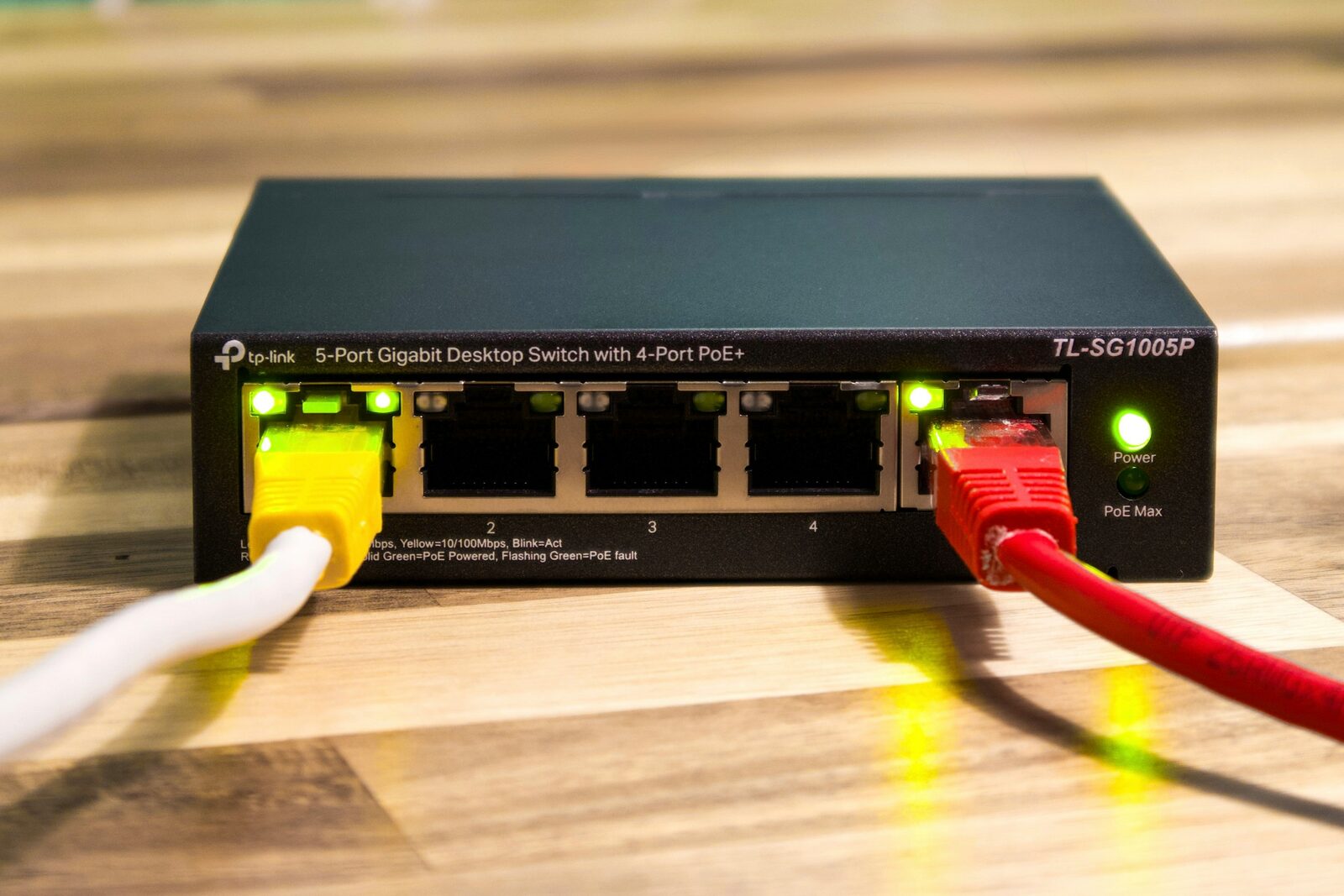
Home router configuration that helps rather than harms
The home router is the choke point of your household network. It controls how devices talk to the internet and how the internet talks back. You do not need to be a network engineer to make it safer, but you do need to avoid a few easy mistakes.
Start with the basics: change the router’s admin password, update its firmware, and use a modern Wi‑Fi standard with a strong password. In the UK many internet providers supply routers with decent defaults, but the admin interface is often still set to a widely known username and password. If a neighbour can guess it, so can a visitor. Updating firmware is dull but important; it closes published vulnerabilities that are actively scanned for on the wider internet.
Next, keep the network simple. Most households do not need remote administration enabled, port forwarding for random services, or universal plug and play (UPnP) turned on by default. UPnP makes it easy for devices to open ports automatically, which is useful for games consoles and video calls but can also be abused by malware to expose services. A balanced approach is to leave UPnP off unless you have a clear need, and then enable it only when you can see what it is doing.
A real-world example: a smart camera app asks you to enable port forwarding so you can watch video feeds from outside your home. That does work, but it also exposes the camera to the internet, where vulnerable models are frequently scanned. A safer design is for the camera to connect outbound to its service and for you to connect to that service with a strong account password and two-factor authentication. This does trade privacy for convenience because a third party is involved, but it avoids the risks of a direct open port on your home network.
Another trade-off is device isolation. Putting smart TVs or speakers on a guest network can stop them seeing your computers, but it also means they may not work smoothly with casting or local media. Isolation reduces risk from compromised devices, yet it can break your daily routines. The choice depends on how much you rely on those devices and how often you have visitors connecting to your network. There is no universally correct answer.
Behavioural fingerprints and how they form
A behavioural fingerprint is the pattern your devices create simply by the way they talk to the network. This includes the time of day you connect, the mix of services you use, the frequency of updates, and the regularity of your browsing. Unlike a cookie, which is a piece of data stored on your device, behavioural fingerprints are inferred from traffic patterns. They can be used by internet providers, Wi‑Fi operators, or anyone who can observe the network path.
For example, a phone that checks the same set of news sites every morning at 07:30, streams a particular radio station on the commute, and uses a fitness app in the evening can be recognised by that pattern even if the device identifier changes. Most of the time this is used for ordinary analytics and service optimisation. It can also be used to link activity across different networks, which matters if you assume that using a café, the train, and your home network creates three separate identities.
Behavioural fingerprints are hard to eliminate because they are a by-product of living a routine life. The mitigation is not to become random for its own sake, but to understand where routine is visible and decide whether it matters. Using the same secure browser on all networks, keeping software updated at sensible times, and avoiding unnecessary background services can reduce the amount of distinctive chatter without making your devices look strange.
Consistency versus randomness
There is a temptation to add randomness to everything: rotate MAC addresses constantly, switch VPN servers every hour, or change devices frequently. These measures can help in specific situations, but they can also create unique patterns of their own. A device that changes identifiers every ten minutes is unusual, and unusual behaviour is itself a fingerprint.
Consistency is not the same as predictability to others. It means keeping your network habits steady enough that they do not broadcast “something special is happening here”. If you use a VPN, use it consistently across your devices and in contexts where it makes sense, such as public Wi‑Fi or when working away from home. If you do not use one, do not toggle it on and off in a way that creates a sharp boundary around particular activities.
A common myth is that constantly changing your MAC address makes you invisible. MAC randomisation helps prevent passive tracking by nearby observers, especially in busy public spaces, but it does not hide your activity from the network operator you are connected to. Nor does it stop fingerprinting based on traffic patterns. Use it because it removes a persistent identifier, not because it makes you anonymous.
The practical balance is to be deliberate. If you are in a low-risk environment, it is reasonable to prioritise convenience and stability. If you are travelling, working on sensitive material, or simply prefer a tighter boundary between contexts, you can choose stricter habits. The aim is not perfect concealment; it is reducing avoidable exposure while accepting that some exposure is built into how networks work.