4.3 Hardware trust and firmware
Most people think of a device as the screen and the operating system you log into. Underneath, there are layers of code that start the machine, handle radio signals, and talk to attached gadgets. These layers are usually invisible, yet they decide what your device will and will not do. That is why “hardware trust” is not only about whether a laptop seems sturdy; it is about whether the earliest code that runs can be relied upon.
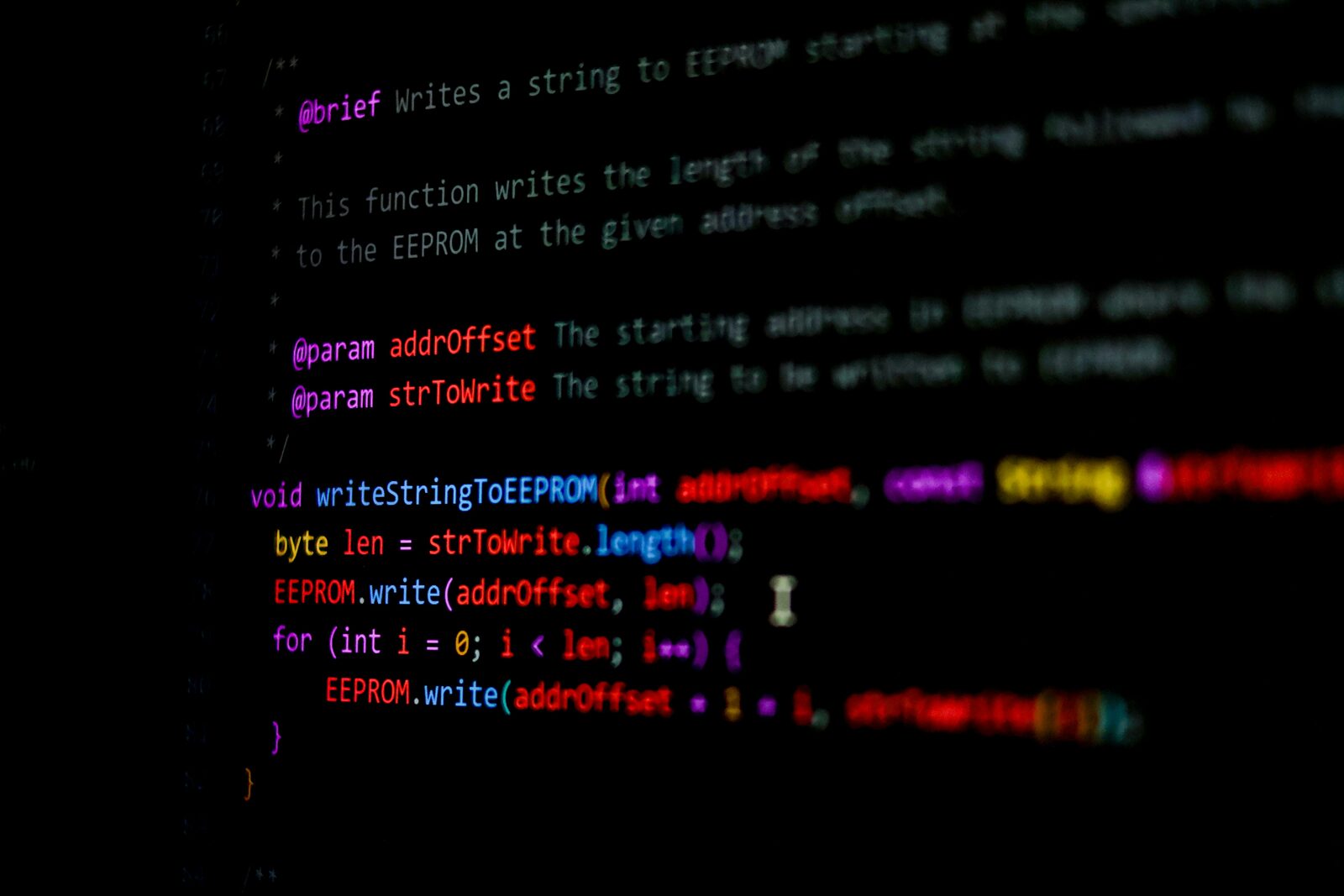
Firmware is the small, specialised software stored on chips. It sits between the hardware and the operating system. When something goes wrong in firmware, it is often hard to detect and harder to repair. That does not mean every device is a trap. It means that the lower you go in the stack, the fewer tools you have to inspect it, and the more you rely on manufacturers, supply chains, and careful maintenance.
BIOS and UEFI persistence
When you press the power button, the machine runs code stored on the motherboard long before Windows, macOS, or Linux appears. Historically this was the BIOS; now it is usually UEFI, a more capable replacement. UEFI can load drivers, show a graphical setup screen, and enforce Secure Boot, which checks that the operating system has not been tampered with. That same power makes it a tempting target for persistence, where malicious code survives a reinstall of the operating system.
A real-world example is a laptop that has been reimaged at work but still behaves oddly: network traffic spikes during boot, or the machine installs a rogue browser extension after each clean install. A compromised UEFI can reintroduce unwanted software every time the device starts, regardless of the operating system image. This is rare, but when it happens it is difficult to diagnose, because normal antivirus tools only see the operating system, not the pre-boot environment.
There are also legitimate reasons for firmware updates: fixing security flaws, improving stability, or adding support for new hardware. In the UK, most people rely on vendor update tools or Windows Update to handle firmware. The common misunderstanding is that “firmware never changes”. In practice, it does, and staying on outdated firmware can leave known vulnerabilities unpatched.
Mitigations revolve around trust and visibility. Use devices that support firmware updates from a reputable source and apply them when stable updates are released. If you are in a higher-risk setting, look for hardware with measured boot or TPM-backed logs that can record what firmware actually ran at startup. These do not guarantee safety, but they make silent persistence harder. The trade-off is complexity: more security features can also mean more ways to lock yourself out if a key or configuration is lost. For many people, the balanced approach is to keep firmware updated, enable Secure Boot if you are not running a custom operating system, and avoid buying machines with unclear provenance.
Baseband processors
In a smartphone, there is a separate processor that handles mobile networks: the baseband. It speaks to the nearest mast, negotiates encryption, and manages calls and texts. The operating system usually has limited control over it. This separation exists for performance and regulatory reasons, but it also creates a blind spot. If the baseband firmware is vulnerable, the main operating system may never notice.
Most people encounter baseband behaviour indirectly. You may see sudden battery drain when signal strength is poor, or notice that the phone connects to a network abroad before you can disable roaming. Those are ordinary baseband functions. The risk is that baseband firmware is complex and largely proprietary, which makes independent review difficult. Attacks on baseband are not everyday events for most people in the UK, but they are possible and have been demonstrated by security researchers. In targeted cases, baseband flaws can be used to intercept or manipulate communications, or to gain a foothold for further attacks.
The practical mitigations are limited because you cannot easily replace baseband firmware. Keeping the phone’s system updates current matters because vendors sometimes bundle baseband updates with OS patches. Using end-to-end encrypted apps for sensitive conversations also helps, because even if the radio layer is compromised, the content remains protected. That does not stop metadata exposure — who you contacted and when — which is part of how mobile networks work. This is a risk that must largely be understood rather than eliminated, and the acceptable level depends on your circumstances.
Peripheral attacks
Modern devices trust what is plugged into them. USB and Thunderbolt are designed to connect keyboards, storage, cameras, and chargers, but they can also expose deep access. Some devices, such as external network adapters or “smart” docks, carry their own firmware. If that firmware is malicious or vulnerable, it can attack the host machine without the user ever opening a file.
A realistic scenario is a company laptop used at a conference, where you borrow a USB-C hub to connect to a projector. A compromised hub could present itself as multiple devices, including a keyboard, and inject commands. Another example is a cheap second-hand USB drive that silently modifies itself to appear as a keyboard and run a script the moment it is plugged in. These are not the same as classic viruses; they exploit trust in hardware interfaces.
The straightforward mitigation is to treat unknown peripherals like unknown software: do not plug them in. Where you must use them, prefer reputable brands, keep their firmware updated if possible, and avoid devices that offer more functions than you need. In higher-risk settings, disable unused ports in firmware settings or use port blockers, recognising that this reduces convenience. The trade-off is practical: locking down ports can break legitimate workflows, and many people do not have the support to manage it sensibly. A measured approach is to keep sensitive work on a device that only uses known, owned peripherals and reserve a separate, less sensitive machine for travel or public environments.
Second-hand device risks
Buying used hardware is common and sensible, but it carries specific risks. A laptop can be wiped at the operating system level while still retaining modified firmware or hardware implants. Most second-hand devices are simply old, not malicious, yet the buyer has no straightforward way to verify what happened before. This is a quiet risk, not a dramatic one.
Common misunderstandings include the belief that a full disk wipe resets everything, or that a factory reset returns the machine to a trusted state. These steps are valuable but do not touch all firmware. On phones, a factory reset usually does remove user data but does not always update or verify baseband firmware. On laptops, a clean install does not reinstall the UEFI firmware.
Mitigations depend on the value of the device and the level of risk you are managing. For ordinary consumer use in the UK, buying from a reputable refurbisher and applying all firmware and OS updates soon after purchase is a sensible baseline. For more sensitive use, consider vendors that provide verifiable firmware update mechanisms and supply chain documentation. Some organisations insist on new devices for high-risk roles to reduce uncertainty. That is not a universal requirement; it is a trade-off between cost and assurance.
There are also practical limits to what you can verify. Independent firmware auditing is expensive and rare. The realistic approach is to reduce unnecessary exposure: do not store your most sensitive accounts on a device you cannot vouch for, enable full disk encryption, and maintain good backup hygiene. If the device behaves oddly — such as persistent changes after a reinstall, unexplained network activity on boot, or firmware update failures — take those signs seriously and consider professional inspection or replacement.